So, you want to hide your email from the NSA’s prying eyes? It’s impossible… but here are some steps you can use to make it harder.
This isn’t theoretical. The NSA has and does intercept this traffic.
Common Points of NSA Interception
The NSA has unlimited resources to compromise your communications. You’re not going to stop them. But that doesn’t mean it should be easy. Below are the easy points of NSA interception. In this example of an email from Mom to Ben the NSA can intercept the email at Mom’s ISP, Mom’s email provider, Ben’s email provider, Ben’s ISP, and any internet hop in between.
I’m going to skip over a lot of important stuff, this guide is not intended for security experts or sysadmins of email systems and how to prevent downgrade attacks, etc. This is meant to be a post about what the average American should do to protect their emails.
Step 1. Client to Server TLS Encryption
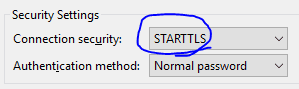

Note, the entire CA (Certificate Authority) system is broken, the NSA could generate a fraudulent certificate from an amicable CA and do a MITM attack and still intercept the email, but now they have to take some effort to do so. The point is security comes in layers, and we need to start at the basics, we’ll get to more advanced security below.
Step 2. Make sure Your Email Provider is Encrypting Server to Server Traffic
In 2013 Google was outraged after finding out the NSA was intercepting it’s server to server traffic. As a result Google started encrypting all internal traffic between servers (Good for Google). Most major internet providers provide server to server encryption. But the problem is not all ISPs use encryption, so it doesn’t do much good if you send an email from a secure service like Gmail to a small-town ISP that has no security whatsoever. Probably the best way to check is to enter in a recipients email address here: http://checktls.com/ and if their email provider’s MX server’s pass all the test they’re probably secure.
Step 3. PGP Encrypt Your Emails
Now, the NSA can still potentially intercept your emails at rest through a court order, through PRISM, or through hacking into ISPs. Your email should be encrypted not only in transit, but also at rest. The best way to do that is to encrypt it using OpenPGP. This means even if the NSA gets a hold of your email they can’t read it (at least not without spending some serious time and money).
PGP (Pretty Good Privacy) isn’t foolproof. It doesn’t encrypt the metadata (the NSA can still see that you sent me an email, they can see when you sent it and where you were) but it does encrypt the content.
How go you get OpenPGP? Right here: http://openpgp.org/software/ It’s free, open source, and there are plugins for just about everything. It works on Webmail, Thunderbird, Outlook, etc. Check the link above for a complete list but here are two common options:
If you use Thunderbird I suggest Enigmail, and if you use Gmail with the webmail interface Mailvelope is a great plugin.
Here’s a very quick getting started guide for Mailvelope below. If you’re not going to use Mailvelope the concept is pretty much the same nomatter what plugin you choose. You’ll Generate a Public/Private Keypair, obtain the public key of the person you’re sending an email to, and send them en encrypted email.
How to Setup Mailvelope for Gmail and Chrome

Next Generate a Key….
I should note that “Password” is traditionally called a Pass Phrase, it should be long, but you don’t ever want to forget it or you won’t be able to read any encrypted messages sent to you. I strongly suggest writing it down and keeping it someplace safe.
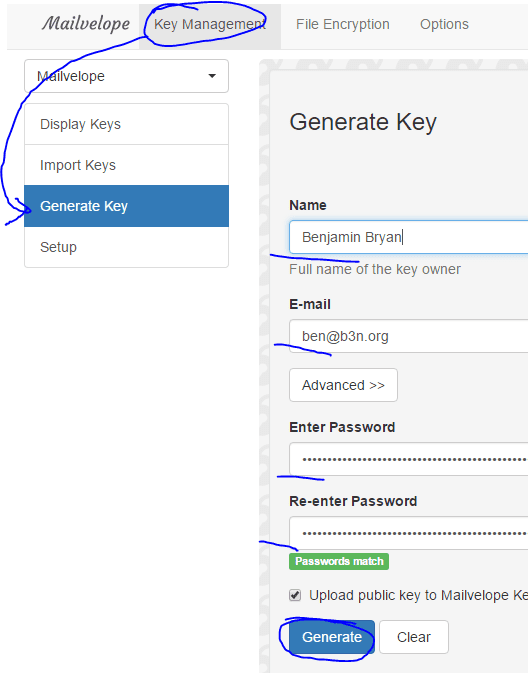
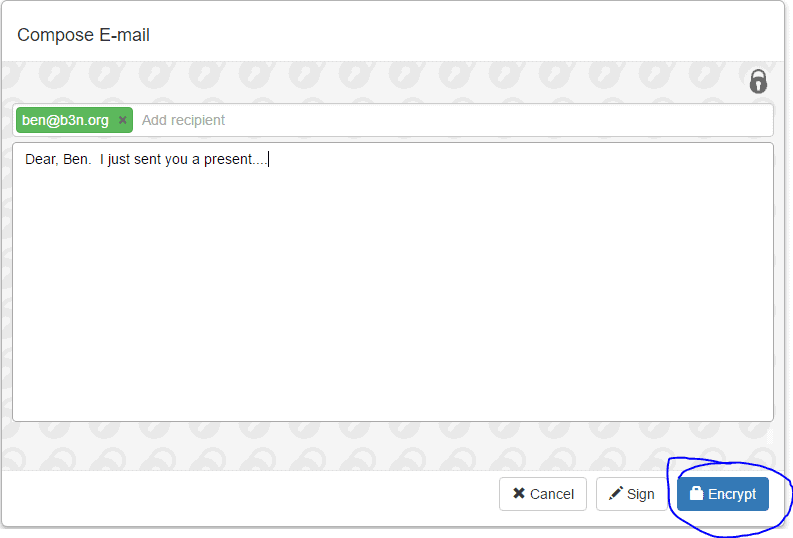
Now, to send an encrypted email to me, you’ll need to import my key. Go to “Import Keys” and type in my email address and hit search. You should click on the keyID: 13E708FC. A key will pop up, click on it to import my key.
Write me a message…
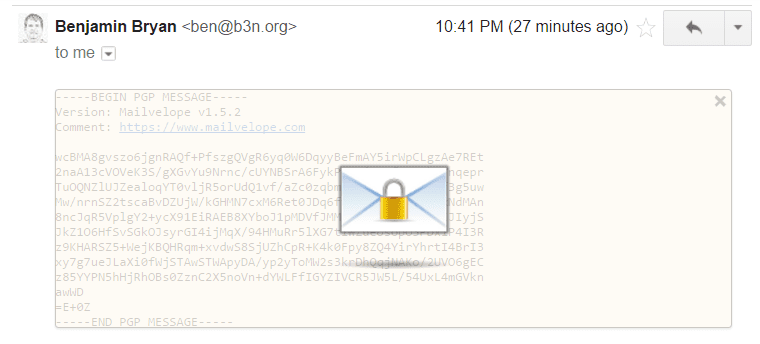
When you receive an encrypted email, it will look like this. Click on it and enter your passphrase to decrypt.
And there you have it. I wouldn’t say this is foolproof…. it doesn’t protect against a lot of other attack vectors…
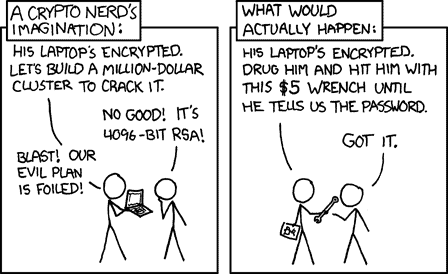
But I say if the NSA is going to intercept my communications it shouldn’t be easy. I want them to spend some effort and money to do so.
For further reading I might suggest https://futureboy.us/pgp.html